Configuring an external OIDC provider
DMS supports to use an external OIDC (OpenID Connect) provider to get authentication services. Authentication settings are specified in the appsettings.json, located in the server folder of the installation folder. Below is an example for setting up an external OIDC provider in appsettings.json:
"ExternalProvider": {
"Enabled": true,
"Name": "Test External OIDC provider",
"ClientId": "test-client-id",
"Authority": "test-authority",
"UsePkce": true,
"ResponseType": "code",
"ResponseMode": "form_post",
"CallbackPath": "/signin-oidc",
"ClaimType": "email"
}
| Setting key: (default) value | Explanation |
|---|---|
| Enabled:false | Enabling authentication service from an external OIDC provider. When set to false, you cannot use an external provider, when set to true, you can. |
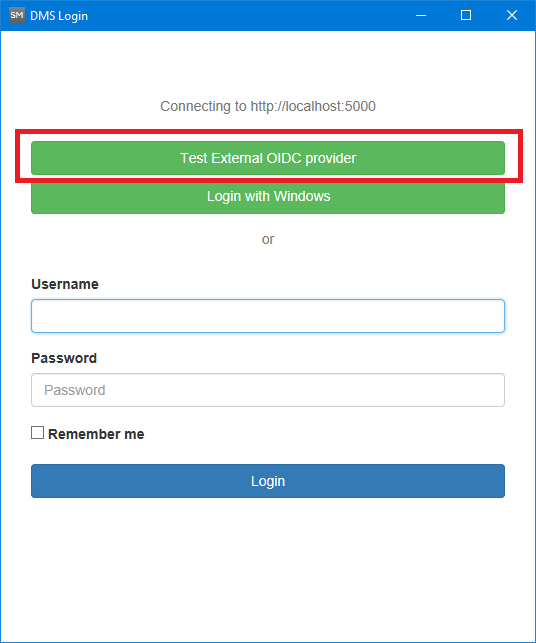
| Name: | Name of external OIDC provider. This name is displayed on the DMS login screen. |
| ClientId: | Unique client id of the external OIDC provider. |
| Authority: | Authority url to make OIDC calls. |
| UsePkce: true | Enables (true) or disables (false) the use of the Proof Key for Code Exchange (PKCE) standard. |
| ResponseType: “form_post” | Response type of OIDC calls. |
| CallbackPath: “/signin-oidc” | The request path within the base path where the user-agent will be returned. |
| ClaimType :”email” | Claim type to request. |
After a successful setup of the external OIDC provider, it will be displayed on the DMS login screen as an additional authentication option (next to the Windows authentication and the username/password login).